Note: Dependabot auto-triage rules are currently in beta and are subject to change.
About GitHub-curated default rules
The GitHub-curated default rule, Dismiss low impact issues for development-scoped dependencies, auto-dismisses certain types of vulnerabilities that are found in npm dependencies used in development. These alerts cover cases that feel like false alarms to most developers as the associated vulnerabilities:
- Are unlikely to be exploitable in a developer (non-production or runtime) environment.
- May relate to resource management, programming and logic, and information disclosure issues.
- At worst, have limited effects like slow builds or long-running tests.
- Are not indicative of issues in production.
Note: Automatic dismissal of low impact development alerts is currently only supported for npm.
The GitHub-curated default rule, Dismiss low impact issues for development-scoped dependencies, includes vulnerabilities relating to resource management, programming and logic, and information disclosure issues. For more information, see "Publicly disclosed CWEs used by the Dismiss low impact issues for development-scoped dependencies rule."
Filtering out these low impact alerts allows you to focus on alerts that matter to you, without having to worry about missing potentially high-risk development-scoped alerts.
The GitHub-curated default rule, Dismiss low impact issues for development-scoped dependencies, is enabled by default on public repositories and disabled for private repositories. Administrators of private repositories can opt in by enabling the rule for their repository.
Enabling the Dismiss low impact issues for development-scoped dependencies rule for your private repository
You first need to enable Dependabot alerts for the repository. For more information, see "配置 Dependabot 警报."
-
在 GitHub.com 上,导航到存储库的主页。
-
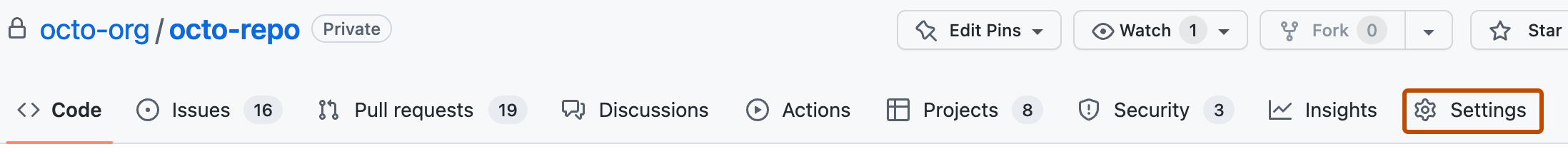
在存储库名称下,单击 “设置”。 如果看不到“设置”选项卡,请选择“”下拉菜单,然后单击“设置”********。
-
在边栏的“安全性”部分中,单击“ 代码安全性和分析”。
-
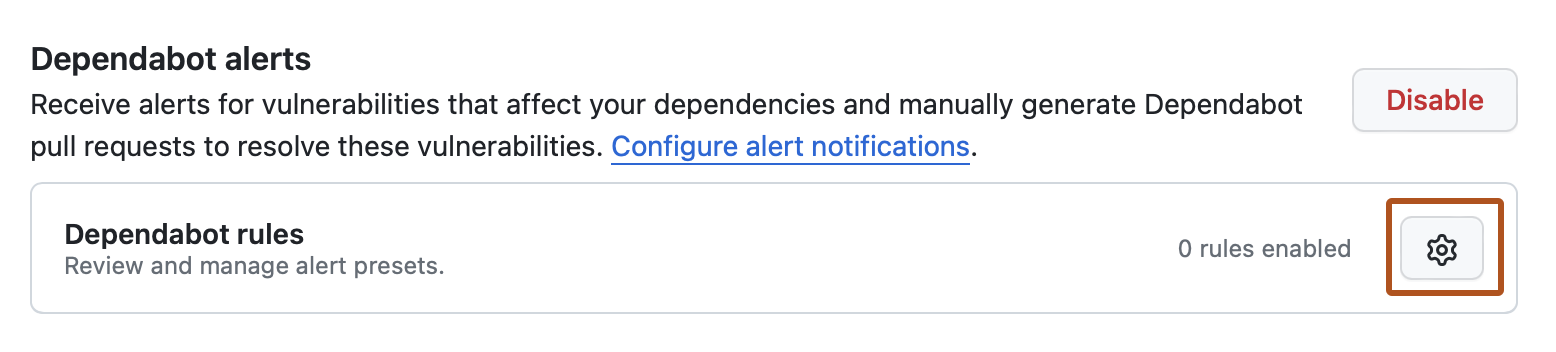
Under "Dependabot alerts", click close to "Dependabot rules".
-
Under "GitHub presets", to the right of "Dismiss low impact issues for development-scoped dependencies", click .
-
Under "State", select the dropdown menu, then click "Enabled".
-
Click Save rule.
Publicly disclosed CWEs used by the Dismiss low impact issues for development-scoped dependencies rule
Along with the ecosystem:npm and scope:development alert metadata, we use the following GitHub-curated Common Weakness Enumerations (CWEs) to filter out low impact alerts for the Dismiss low impact issues for development-scoped dependencies rule. We regularly improve this list and vulnerability patterns covered by built-in rules.
Resource Management Issues
- CWE-400 Uncontrolled Resource Consumption
- CWE-770 Allocation of Resources Without Limits or Throttling
- CWE-409 Improper Handling of Highly Compressed Data (Data Amplification)
- CWE-908 Use of Uninitialized Resource
- CWE-1333 Inefficient Regular Expression Complexity
- CWE-835 Loop with Unreachable Exit Condition ('Infinite Loop')
- CWE-674 Uncontrolled Recursion
- CWE-1119 Excessive Use of Unconditional Branching
Programming and Logic Errors
- CWE-185 Incorrect Regular Expression
- CWE-754 Improper Check for Unusual or Exceptional Conditions
- CWE-755 Improper Handling of Exceptional Conditions
- CWE-248 Uncaught Exception
- CWE-252 Unchecked Return Value
- CWE-391 Unchecked Error Condition
- CWE-696 Incorrect Behavior Order
- CWE-1254 Incorrect Comparison Logic Granularity
- CWE-665 Improper Initialization
- CWE-703 Improper Check or Handling of Exceptional Conditions
- CWE-178 Improper Handling of Case Sensitivity
Information Disclosure Issues
- CWE-544 Missing Standardized Error Handling Mechanism
- CWE-377 Insecure Temporary File
- CWE-451 User Interface (UI) Misrepresentation of Critical Information
- CWE-668 Exposure of Resource to Wrong Sphere